Any attack is usually non-intended vulnarabilities. Same argument applies to any software, like nano, if it can open doors to your system.
Doctor xNo
Check out cVn! Where you can watch user-sourced pre-listed synchronized youtube videos while earning some XNO (Nano) for it, or queue your own youtube video of choice to the list for some crypto-dust, all while chatting in a chatroom with the rest of the viewing community. http://cryptovision.live
- 1 Post
- 135 Comments
I appreciate all the answers on what started out to mostly be a joke (the first comment, I’m not saying the rest was, I actually do mean my follow-up discussions and am enjoying them more than I should). 😅
Anyway, first I must disagree with sudo being useless in a single-user environment since some services have non-user (nologin) accounts as which you still need to run things sometimes, so sudo is commonly useful in single-user environments (though you could technically go set bash for those, I suppose.)
But yeah, I’m already used to “bad practices” as I have been using linux for 24 years now (when it still was it’s predecessor ‘pico’ 😅) (I said over ‘10’ years in an earlier comment, but I just realized I’m 40 and still calculated from 30. 😂 Wishful thinking. 😅) in what is assumed a bad practice, not only without any problems, but even because it never gave me problems.
Might be an age thing too, but I hold on to ease of use over best-practice, especially if it hasn’t failed me in two decades and a half. I think it would take an actual attack on me abusing this behavior for me to stop doing it by now… And even then, I installed linux so many times in my life, even that seems more musclememory and not such a hassle anymore… 😅 At least I could make use of my backup system for once then… 😅
You assume this malicious code is lame enough not to gain root itself with a modified su.
Indeed… Hence why I use ‘sudo nano’. 😜
Wouldn’t that logic count for anything, including sudo itself?
But, in that example:
If I’m the admin it doesn’t matter I use it.
If I’m not it’s not my problem that I could get more privileges than allowed. I’d probably even use the possibility then. 😅
So it poses a risk if you allow none-admin users to do that on your system, but I still don’t see why I must choose to not use nano as root myself. 😅
Anyway, good practice to me is ease-of-use instead of with 7 protections against things that rarely happen.
Like, I’m pretty sure you are better protected from burglars if you also lock all doors inside your house, but I’m definitely not doing that either. 😅
Edit: Also, if you have users on your system, just chroot/vroot/lxc them, so they be free to ‘sudo nano’ too… 😅
So for any supposedly malicious activity (infected) it wants to do, it just has to hold until you save and give admin access? 😅
I just have a root custom config too. 🤷♂️ This even allows me to easily use different configs for root than for the user.
Made with ‘sudo nano’, fyi. 😂
Let me rephrase my question:
Why would I not want to open nano as root?
No offense, but that sounds like more OCD behavior. 😅 I don’t need or want protection against myself, and I even loath the whole “that’s not how you’re supposed to do it”-mentality of linux (where when commands know very well what you want, instead of doing it, just tell you you forgot something). 😅
 1·2 years ago
1·2 years agoThis is going a bit too far now, imho.
An example that I encountered myself today:
Google:
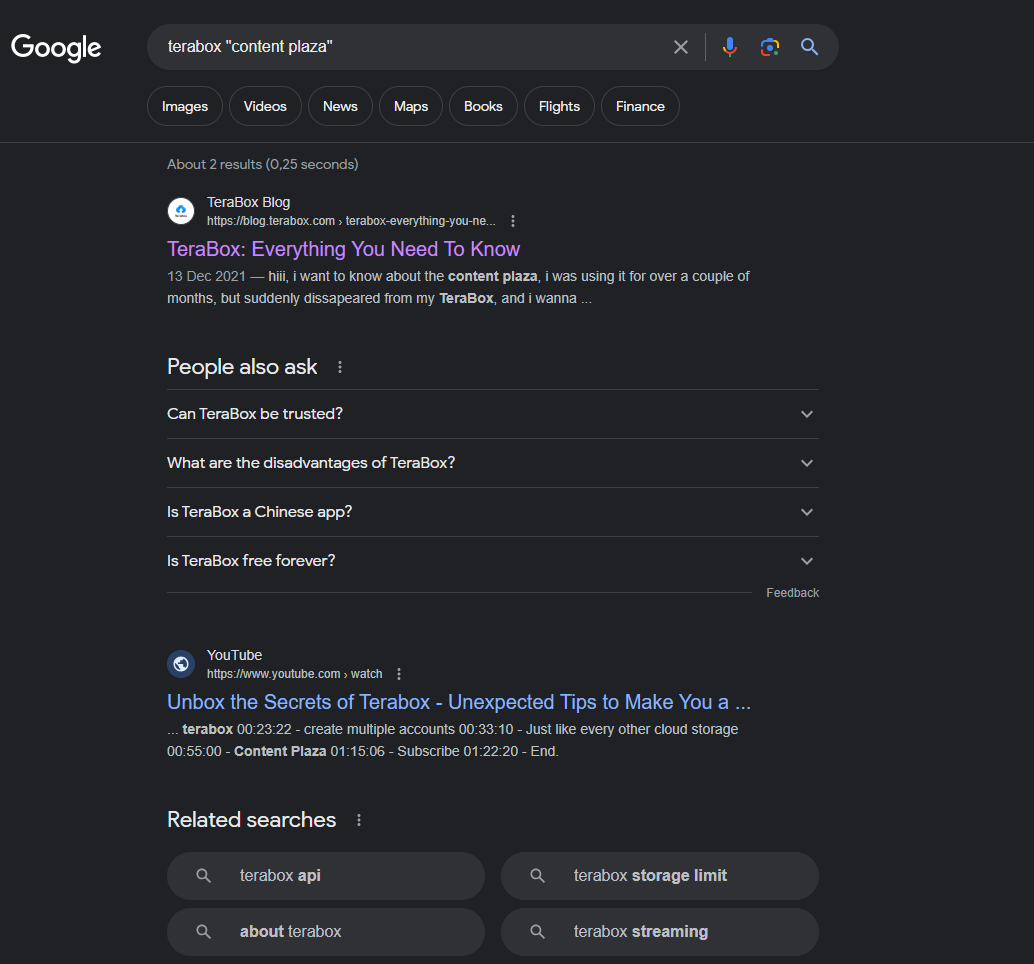
Unfiltered search engine (in this case Yandex):
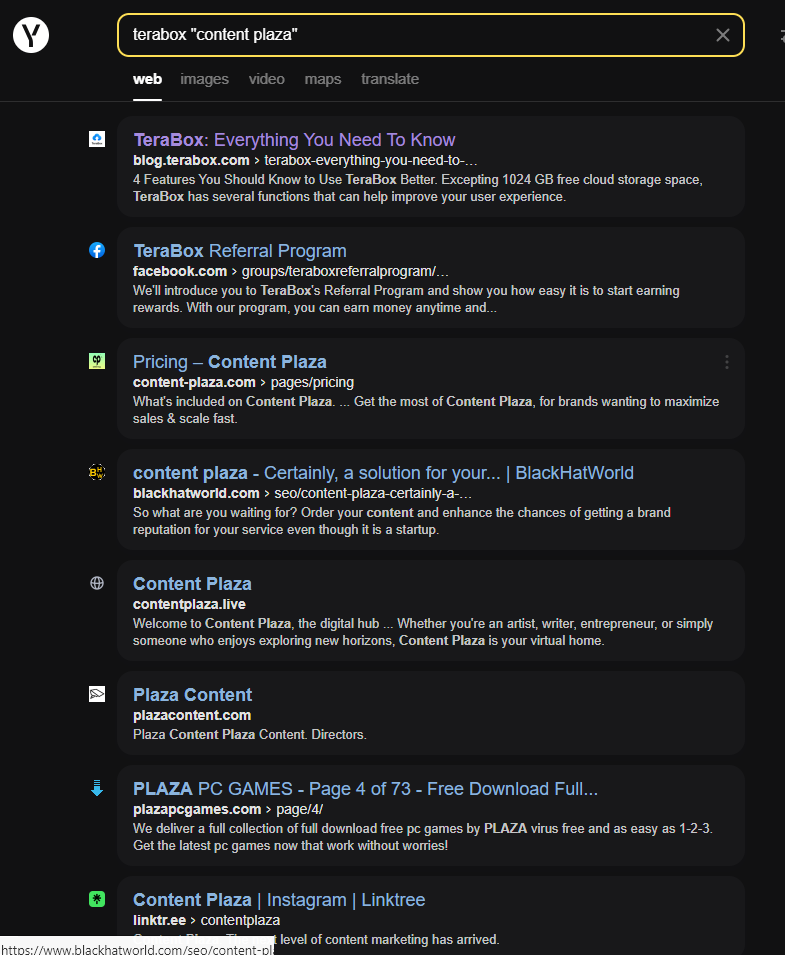
Like, WTF Google!
Edit: Woops, did I reopen an 18d-old thread? 😅
 4·2 years ago
4·2 years agoOr to the existence of copyrights and how they work (against progress).
Why?
Files from user: nano
Files from root: sudo nano
Files from another user: sudo nano (and if new sudo chown after)… 😂
Never had any problems with this in over 10 years… 😅😂
Just send out your local Karen.
 42·2 years ago
42·2 years agoAnyone can link this “app” separately? Cause I disabled my AndroidTV launcher in exchange for a customizable launcher on my box and since that not only opened the box completely to me but also got rid of all the nasty “built-in” annoyances the company providing it added, I’m definitely not switching back.
Might even eventually return the box like this to my ISP in the end, cause I didn’t do anything wrong: I didn’t need root to get the above done, just used unrooted wireless adb… 😅
Edit: nm, I’m not American, so it won’t stream here anyway. 😅
 3·2 years ago
3·2 years agoSee link as comment to myself above. 😉
 1·2 years ago
1·2 years agoI made a comment to my own comment above with the link. 😜
 3·2 years ago
3·2 years agoFor all those asking how or with what:
https://play.google.com/store/apps/details?id=com.pspace.vandroid
 6·2 years ago
6·2 years agoI run a full Android Emulator inside my Android since Android 8.1.1 and I have yet to find any limitation to virtualization. I run modded games there, as also sus apps or things I want to play but know has a trojan or virus inside that I can’t get out. Currently the lowest device I’m using that has it installed is still an Android 9.1.0. 😅
So, I’m guessing they either just mean better Android functionalities using it or improved access to hardware. Other than those I can’t see what they could add, cause the full functionality already exists quite some time… 😅




Yeah, well, as you said: it’s probably fixed by now, but I used to have a universal su that would work on any armv7 linux (so basically every phone back then, but also on my armv7 little laptop I had at the time…) with which I was able to easily root any phone by putting it in /data/local and making it bootable, then using full path to move any Android root files in place (though I did also just copy that su itself to /system/bin for root on cheaper phones sometimes, which is just playing with fire as it basically makes any root action unseen and allowed. 😂). That did work for years though, but that’s probably cause Android minimizes the linux and never actually updated the kernel so much, and the laptop’s flashed OS was something altered with also very little updates. And ARM was still quite new to the public too. 🤷♂️
I remember I came across it in the rooting package for my Kindle Fire and only found out it could do that by accident,… 😅 It couldn’t change user, though, it had only 1 use without parameters, which resulted as if you do a ‘sudo su’ if you remove the sudo password-requirement.
Hence why I used the example. I wasn’t being limitative to it, though. There’s so many things that could screw you if it has a vulnerability, if it happens I very much doubt it’ll be through nano, though.