Intel breathes a sigh of relief as the spotlight moves off of them for a beat.
It was really just a matter of time before someone figured a way to exploit those stupid deep management engines. It was so predictable.
And each intel chip runs a minix system behind the scenes that I’m sure someone will soon find a way to play with if it’s not already compromised.
And each intel chip runs a minix system behind the scenes that I’m sure someone will soon find a way to play with if it’s not already compromised.
There was a big story of an expoit of the Intel ME already. I think it was this: https://www.intel.com/content/www/us/en/support/articles/000025619/software.html from Positive Technologies at BlackHat 2017
Except the AMD exploit requires ring 0 access and is almost irrelevant to most users, whereas the Intel issues are physically destroying people’s computers. The scale of the issues are utterly incomparable.
I’m much more angry with whatever dipshit at AMD decided to revoke permission for ZLUDA, and that they haven’t yet been fired.
People grant kernel access all the time without thinking. Video game anti-cheat is a good example. It’s a pretty potent vector of attack since you can never trust these companies to keep themselves secure.
Apex Legends and Genshin Impact being a good example of this.
The Apex Legends hacking situation was unrelated to the anti-cheat despite initial reports. It didn’t stop the hack but it also wasn’t the vector for the attacks.
Genshin Impact’s anti-cheat however was an unmitigated disaster.
The Apex Legends hacking situation was unrelated to the anti-cheat despite initial reports
you’re right, thanks for the clarification! https://inv.tux.pizza/watch?v=lzW4SDm0yWM
ZLUDA was probably taken down to protect AMD from being sued by Nvidia.
Didn’t the author confirm the takedown came from AMD and not NVidia? AMD isn’t responsible for third party software running on their hardware.
Although, IIRC they either sanctioned it or provided some initial funding, which might have put them in a more culpable position. Still, I’m pretty sure the takedown came from AMD, and it doesn’t make sense that they’re doing NVidia’s policing for then.
They were paying for its development for about a year and a half.
what’s ZLUDA? can you ELI5?
ZLUDA was an open source translation layer for CUDA. So basically developers could take code from projects written for Nvidia’s CUDA and use ZLUDA to run them on other hardware. Originally the dev was focused on Intel but AMD started paying him and he focused on AMD hardware. They stopped funding him earlier in the year and now it appears AMD legal has gone back on their earlier permission for him to keep distributing the code.
deleted by creator
“FUCK!” - Intel execs
No way that Intel sat on this for years until they needed it for PR.
I’ll bet the Intel management engine is just as “vulnerable”. The only context this is likely a concern is large scale corpo deployments, without verified supply chains to the source. Love how the security researcher handwaves that there’s “plenty of existing exploits” that can be used to install the exploit into the SMM, without giving any suggestions of how.
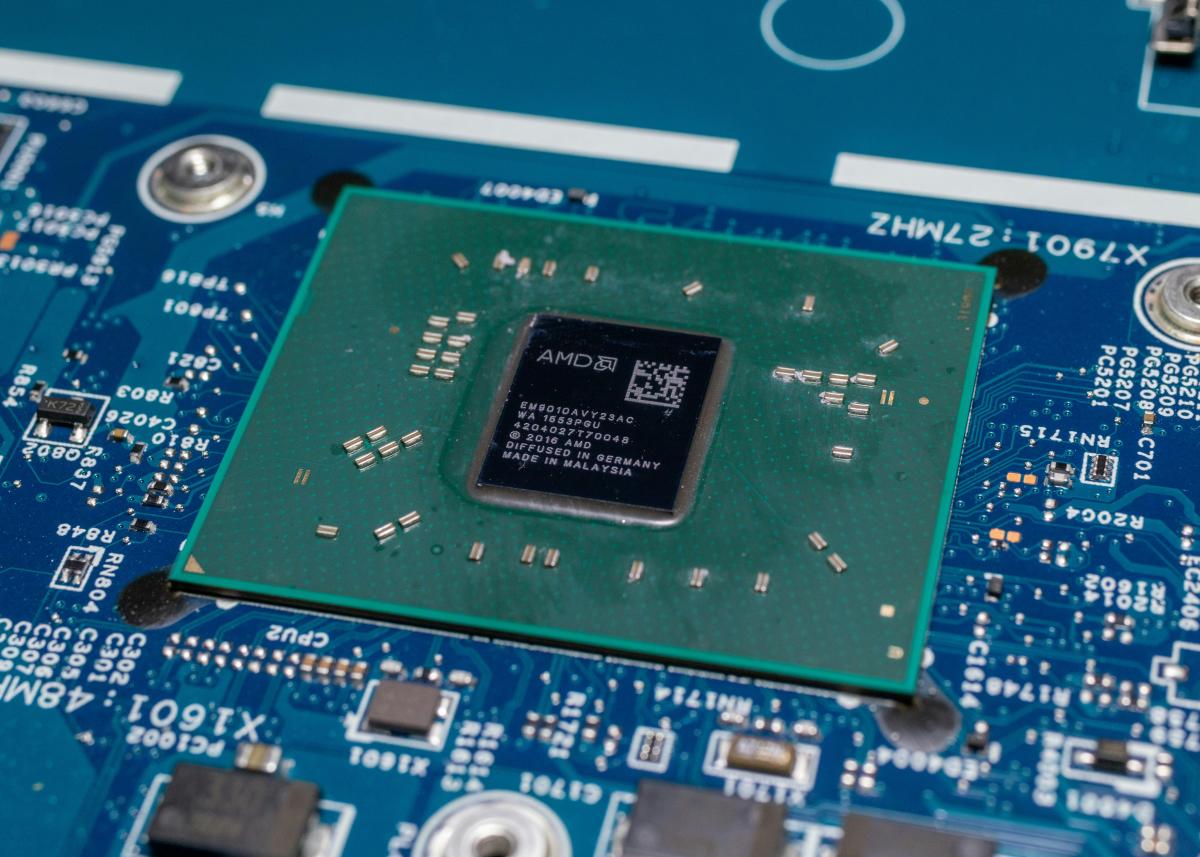
Sinkclose
Impacted systems: https://www.amd.com/en/resources/product-security/bulletin/amd-sb-7014.html
Original presentation details. https://ioactive.com/event/def-con-talk-amd-sinkclose-universal-ring-2-privilege-escalation/
This is a big f****** deal. If you get kernel access to a system, which is not uncommon, you can install a persistent back door that subverts the rest of the system forever. That’s huge. It does not require physical access, requires kernel access… different things
Steam games that ask for admin privileges, a USB stick that boots, normal virus infection that can never be uninstalled,. persistent RAT…
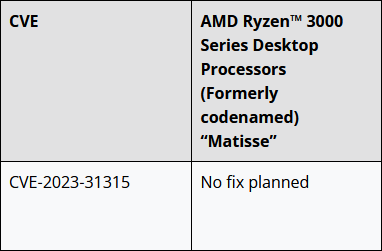
What the heck? Then get to planning you dicks?
There is no possible fix.
For all the others on the page they are planning fixes, only Mattisse has this. Is there something special about Matisse compared to the others?
Now onto some better news. Despite being potentially catastrophic, this issue is unlikely to impact regular people. That’s because in order to make full use of the flaw, hackers would already need deep access to an AMD-based PC or server. That’s a lot of work for a random home PC, phew, but could spell trouble for corporations or other large entities.
Hmm.
It does mean that any secondhand computer or CPU (or even CPU from a sketchy source) could be compromised prior to being physically sold.
I have worried a bit before about the physical supply chain. Consider this case, earlier in the year, about someone selling counterfeit Cisco hardware (not intending to compromise computers, just make a buck):
“Aksoy sold hundreds of millions of dollars’ worth of counterfeit computer networking equipment that ended up in U.S. hospitals, schools, and highly sensitive military and other governmental systems, including platforms supporting sophisticated U.S. fighter jets and military aircraft,” said Principal Deputy Assistant Attorney General Nicole M. Argentieri, head of the Justice Department’s Criminal Division. “Criminals who flood the supply chain with low-quality networking equipment from China and Hong Kong harm U.S. businesses, pose serious health and safety risks, and compromise national security. This case—one of the largest counterfeit trademark cases ever prosecuted in the United States—demonstrates the Criminal Division’s commitment and capacity to prosecute the most complex counterfeiting schemes and bring the perpetrators to justice.”
“Through an elaborate, years-long scheme, Aksoy created and ran one of the largest counterfeit-trafficking operations ever,” said Attorney for the United States Vikas Khanna for the District of New Jersey. “His operation introduced tens of thousands of counterfeit and low-quality devices trafficked from China into the U.S. supply chain, jeopardizing both private-sector and public-sector users, including highly sensitive U.S. military applications like the support platforms of U.S. fighter jets and other military aircraft. Yesterday’s sentence, made possible by the investigation and prosecution of this office and our department and agency partners, now brings Aksoy to justice and holds him accountable for the breathtaking scale of his operation.”
According to court documents and statements made in court, Aksoy ran at least 19 companies formed in New Jersey and Florida, as well as approximately 15 Amazon storefronts and at least 10 eBay storefronts (collectively, the Pro Network Entities). The Pro Network Entities imported from suppliers in China and Hong Kong tens of thousands of low-quality, modified computer networking devices with counterfeit Cisco labels, stickers, boxes, documentation, and packaging, all bearing counterfeit trademarks registered and owned by Cisco that made the goods falsely appear to be new, genuine, and high-quality devices manufactured and authorized by Cisco. The devices had an estimated total retail value of hundreds of millions of dollars. The Pro Network Entities generated over $100 million in revenue from the scheme, and Aksoy personally received millions of dollars.
I remember that that hardware made it into even Cisco’s own authorized partners’ inventory.
And that’s not something that’s gonna be far up in the supply chain. People don’t build Cisco hardware into a lot of other products.
So you gotta wonder what can happen if someone has a good way to undetectably compromise CPUs and insert them into the supply chain.
It does mean that any secondhand computer or CPU (or even CPU from a sketchy source) could be compromised prior to being physically sold.
It’s worse than that, any AMD chip from any source except maybe AMD directly is suspect. Mine is a few years old from Amazon supposedly new, for all I know it came compromised and is sitting there doing what I tell it to until it triggers and I won’t even know when or if it happens.
If I understand it correctly, the chip has the vulnerability, but the malware would be installed on the motherboard in the form of a bootkit. So getting a used CPU is not a threat, but getting a used motherboard is (and kind of always has been) a risk.
It allows for adulteration of firmware, the CPU has firmware. 🤷
CPU firmware exploits are incredibly rare, if there even are any that exist beyond proof-of-concept. The chances of getting an infected CPU from this is so unlikely it’s practically impossible.
You forget that the CPU has a nanny CPU built in these days.
Which, again, is an incredibly unlikely attack vector unless you have some government secrets on your computer. And chances are that any attack through the IME or PSP is trying to do an implant into the UEFI/BIOS and not the processor itself.
Physical access is root access, always has been
This post was sponsored by INTEL™️
/jk
How long were you sitting on that one waiting for the perfect moment?
Which is by pure chance also what the person said who got the exploit list from Intel
Wouldnt be surprised if the researchers were Intel researchers.
*100 employees were fired too allocate budget for this sponsorship